“Cryptowall”—the cause of Luke’s all-nighter—is one of the more well-known families of crypto-ransomware, a category of viruses that encrypts files on a victim’s computer and keeps them locked until the victim pays a set ransom. If you don’t pay the criminals who spread the virus—up to $5,000 per user, according to the FBI—you’ll lose the files forever.
In other words: imagine you arrive at your office one day to find all your computers padlocked, and a man in a mask demanding $5,000 per user to give you the key. That’s what ransomware is like.

The next great threat to business IT?
Ransomware attacks are growing more frequent thanks in part to two technology trends: the increasing processing powers of computers (which are now so powerful that they can encrypt their own files in a matter of hours) and the rise of anonymous payment systems such as Bitcoin (which make it easy for criminals to accept payment without fear of being traced).
Numerous tech publications have listed ransomware among the biggest digital threats facing businesses today. This is due to its capacity to slip through corporate security and its potential to replicate itself across a corporate network. Even Apple users aren’t immune: the first ransomware targeting Macs has recently been spotted. More is sure to come.

If your company gets infected, you face two very hard choices: either spend multiple days recovering the locked files from backups—during which time you’ll endure user downtime, lost sales and angry customers—or pay ransom to an organized crime syndicate.
(Even then, you still need to wipe and restore your computers to remove the virus. Without a business continuity plan in place, infected users will experience downtime regardless. More on that below.)
Just ask the Hollywood Presbyterian Medical Center
The employees of the Hollywood Presbyterian Medical Center can tell you what it’s like. This February, they were forced to take their PCs offline so I.T. could contain a ransomware outbreak and restore their files. They spent 10 days relying on fax machines and paper charts. They made unwanted headlines in the New York Times, the BBC and countless other publications. In the end, they ended up paying $17,000 in ransom, just to avoid even more protracted downtime.
This report helps you understand the true cost of ransomware, learn some basic prevention and containment techniques, and plan for business continuity to avoid downtime in the increasingly likely event that your business will get hit.
[row][col size=”1/2″ ]RESERVED FOR VIDEO[/col][col size=”1/2″ ]RESERVED FOR LINK TO ARTICLE[/col][/row]
The scope of the threat
Intermedia commissioned an independent research firm to conduct a survey of nearly 300 IT experts about the crypto-ransomware threat. The survey respondent panel was carefully screened to include experts that consult with businesses of all sizes on setting up and maintaining IT infrastructures. These are the men and women who are on the front line of business IT challenges such as ransomware.
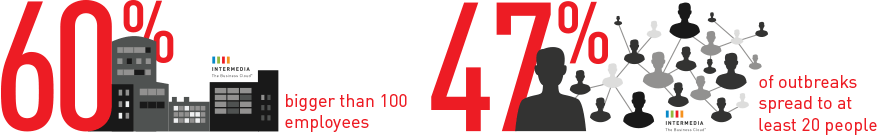
The full results of the survey are available in Intermedia’s 2016 Crypto-Ransomware Study. This report will focus on three key findings: 1) The biggest cost to businesses is downtime, not the ransom payment; 2) Ransomware is targeting bigger businesses and spreading within corporate networks; and 3) A widespread lack of business continuity planning is what makes ransomware so dangerous (and so lucrative for criminals).
Paying ransom is the least of your worries
When asked to name the business impact of ransomware outbreaks that these consultants have assisted with first-hand, they listed the actual cost of the ransom last. In other words, contrary to popular belief, the actual ransom payment is far from the worst damage caused by ransomware.
Downtime lasts for days
A computer that is discovered to have ransomware must immediately be isolated from the corporate network in the event the malware is programmed to spread. This leaves users without access to their computer while IT contains the virus and restores the device. But even if they can get to their files through alternate devices, the files themselves are encrypted and thus unusable.
There are business continuity solutions for ransomware (more on that below), but the survey results suggest that few businesses have any solution in place: 72% of business users lost access to data for at least two days, and 32% lost access for five days or more.
[row][col size=”1/1″]
How many days were the infected employees locked out of their files?
[/col][/row]
Downtime occurs even if you pay the ransom
An infected computer must be wiped and restored to clear it of the malware, even if you pay the ransom to recover your files. And that takes time. 52% of experts reported that the wipe-and-restore process took two or more days for the infected devices. (Even worse: 19% of companies that paid the ransom still didn’t get their files back.)
Bigger businesses are being targeted
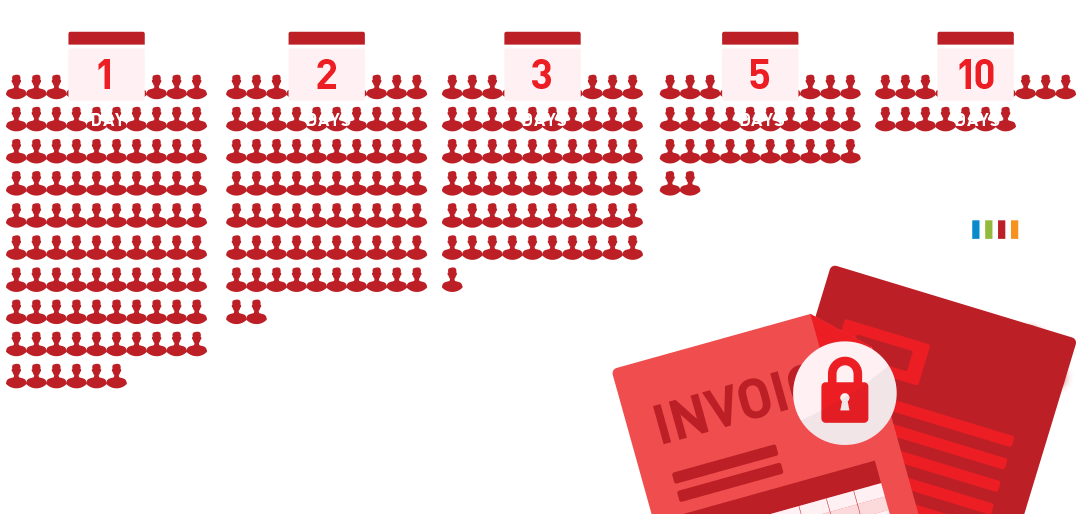
The criminals behind ransomware are going after businesses of all sizes. 89% of the businesses hit by ransomware had 10 employees or more, while 60% had more than 100 employees. And ransomware tends to hit multiple users at once; 75% of outbreaks affected three or more people, and 47% of outbreaks spread to at least 20 people.
Ransomware is a growth industry
43% of IT consultants have had customers fall victim to ransomware. 48% saw an increase in ransomware-related support inquires in the past year—across customers in 22 different industries.
What are the key takeaways?
[row][col size=”1/2″ ]RESERVED FOR VIDEO[/col][col size=”1/2″ ]RESERVED FOR LINK TO ARTICLE[/col][/row]
Preventing ransomware
Like most forms of malware, ransomware infections may arrive through malicious web pages, infected thumb drives, or other common attack vectors. But the most common infection vectors are email-based—often using the same techniques found in phishing emails.
“Phishing” is when criminals send a seemingly legitimate email that disguises a malware-laden attachment or link to an infected website. Criminals often use phishing to trick users into submitting sensitive information such as passwords or credit cards; but these days, they’re also using it to spread ransomware.
In a recent study1, 94% of people couldn’t tell the difference between a real email and a phishing email 100% of the time. When study participants received an email that was spoofed to appear as if it was sent by UPS, 62% trusted it enough to click the link.
Protection against ransomware goes hand-in-hand with phishing prevention. Here are your top three activities:
[row][col size=”1/3″ ]
Protect
Your email defense should go beyond spam and virus scanning. It should also be sophisticated enough to recognize and block phishing attempts.
[/col][col size=”1/3″ ]
Educate
Technology can only go so far to stop phishing. Employees and executives have to be trained to spot phishing emails before they click.
[/col][col size=”1/3″ ]
Prepare
While you need to block every single attack, the criminals only need to succeed once. Plan in advance for how you’ll contain the damage before they do finally break through.
[/col][/row]
1 McAfee: Phishing Deceives the Masses: Lessons Learned from a Global Assessment
[row][col size=”1/2″ ]RESERVED FOR VIDEO[/col][col size=”1/2″ ]RESERVED FOR LINK TO ARTICLE[/col][/row]
Containing a ransomware outbreak
[testimonial author=”Luke Skibba, @Gigabitgeek” avatar=”
” role=”CEO” link=”#” ]After shutting down the computer of the affected user and taking her off the network, we determined she had been hit with the CryptoWall ransomware. We had 90 percent of our files be encrypted. This impacted every user in our whole company.[/testimonial]
Ransomware is hard to spot while it’s encrypting user files. The user may notice his or her machine acting strange during the encryption process: file extensions will change, files won’t open, or the computer’s fan may whir loudly as the processor copes with the computing demands of encryption. But the average user may not recognize the danger until the ransom demand finally appears.
This means that IT typically doesn’t learn about the infection until after the damage has begun and the malware is already inside the network.
At this point, IT’s priority has to be to contain the virus and prevent if from spreading within the network. More sophisticated ransomware variants may attempt to propagate. Malware of all forms has been observed to send malicious messages using the user’s email or chat clients, or even to deposit infected files in open shared folders on other users’ computers.
“The first thing we would do is get the machine off the network,” says Susan Tait, Intermedia’s Director of IT, describing our response to a hypothetical ransomware attack. “We always have to assume that the malware could make use of an internet connection – that it’s sending information back to the criminals, or spreading itself to other users. In the worst-case scenario, we may even temporarily turn off network access for the entire office until we get the outbreak under control.”
Top three ransomware containment tips:
[row][col size=”1/3″ ]
Isolate the infection
Your top priority is to keep the infection from spreading. Remove infected machines from the network. Shut down the network if you have to.
[/col][col size=”1/3″ ]
Size up the outbreak
Figure out the scope of your infection—the virus type, how many machines, how much data, etc. Consider contacting law enforcement.
[/col][col size=”1/3″ ]
Find the attack vector
Identify the source of the virus so that you can patch any security weaknesses or holes. Otherwise, you may remain vulnerable to more outbreaks in the future.
[/col][/row]
[row][col size=”1/2″ ]RESERVED FOR VIDEO[/col][col size=”1/2″ ]RESERVED FOR LINK TO ARTICLE[/col][/row]
Business continuity during a crypto-ransomware outbreak
“Business continuity” is the ability for the business to continue operations even while a disaster is ongoing.
Many businesses have plans in place for natural disasters, power outages or other disruptions. Fewer have “e-crisis” response plans for cyber threats such as ransomware. That’s one of the reasons ransomware has been so disruptive to businesses and so profitable for criminals: business continuity solutions have not previously existed.
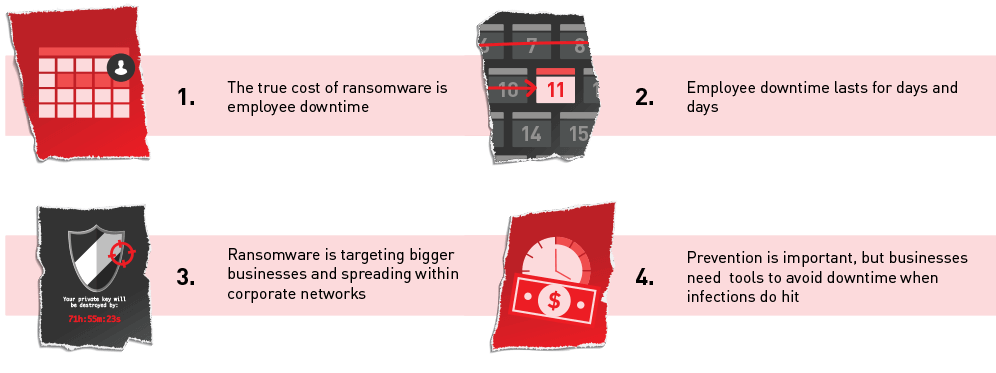
In order for users to continue working during a ransomware outbreak, two capabilities are required.
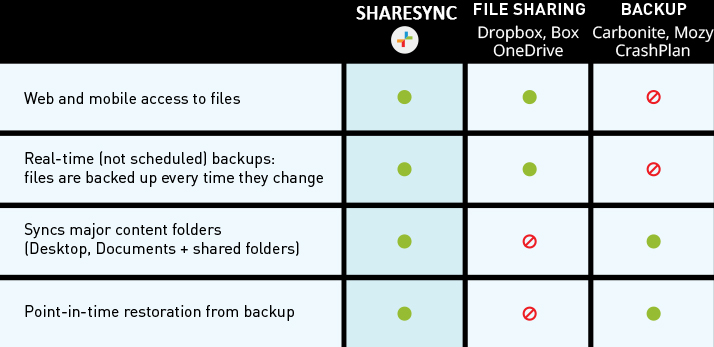
Some of these capabilities exist in file sync and share products. Other capabilities exist in backup products. Ransomware has been so lucrative for criminals because these two capabilities have never before been present in a single product.
[row][col size=”1/4″ ] [/col][col size=”1/4″ ]
[/col][col size=”1/4″ ]
File Sync & Share’s Weakness: You can’t easily roll back to clean files.
When ransomware encrypts the files in your online storage folder (Dropbox®, Box®, Google Drive®, etc.), the encrypted files sync up to the cloud. So online versions are also locked. While you can perform rollback on a file-by-file basis, you can’t instantly perform a ‘mass rollback’ to revert your entire file archive to uninfected versions. Some providers offer this service through a support request, but the process takes hours or days.
[/col][col size=”1/4″ ]
Backup’s Weakness: You can’tinstantly access clean files.
Restoring from on-premises backup takes hours. Restoring from cloud backup takes even longer. For example, Carbonite’s® restore rate is 10 Mbps, which means a 50 GB file archive will take around 12 hours to restore.1 In all cases, the user is completely idled while the backup is restoring.
[/col][col size=”1/4″ ] [/col][/row]
[/col][/row]
1 Carbonite.com: Average Restore time. http://support.carbonite.com/articles/Personal-Pro-Mac-Windows-Average-Restore-Time
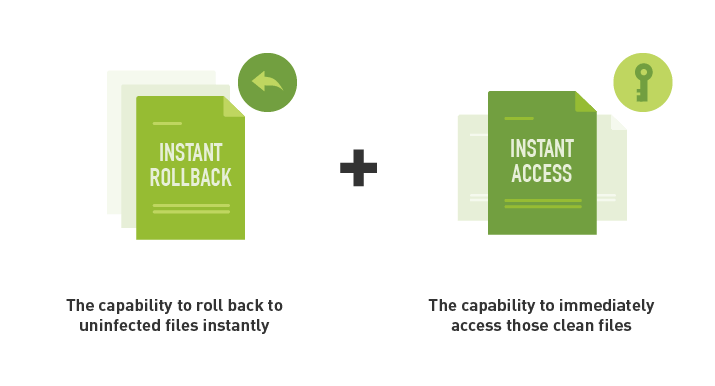
What’s needed to establish business continuity during an outbreak is for these two capabilities—instant rollback and instant access—to be present in a single product.

ShareSync by Digital6 Technologies
2-in-1 file sharing & backup offers instant rollback and instant access, enabling users to keep working during a ransomware outbreak
[testimonial author=”Luke Skibba, @Gigabitgeek” avatar=”
” role=”CEO” link=”#” ]
One of the biggest pain points for any company is downtime. Being able to go from weeks or days to minutes will change the game of fighting ransomware for Digital6 Technologies’s ShareSync customers.
[/testimonial]
ShareSync is a universal file management tool: it combines real-time backup and file sharing into a single product.
This 2-in-1 feature set enables file collaboration similar to Box and Dropbox alongside a complete file backup and recovery across any failure scenario, like Carbonite and Mozy.

Among its feature set is the ability to roll back a user’s complete file set to any point in time. It’s a simple, do-it-yourself process: you select the folder(s) you want to restore, select the target point in time—down to the minute—and press the button. Your folders are instantly rolled back to their state at that point in time. A user can then access those files instantly through the web or mobile devices, even as they’re re-syncing to the user’s computer.
This is how ShareSync enables business continuity during a ransomware outbreak: instant rollback and instant access.
In the event of a ransomware outbreak, this combination of features—which can only be found in a 2-in-1 file sharing and backup service—keeps infected users productive. It also takes the pressure off of IT. Instead of being pressured by users who are demanding their computers, they can take the time they need to carefully contain the virus and patch any security holes.
ShareSync is designed with enterprise-grade control and security to offer at-rest and in-transit encryption, remote wipe of ShareSync data off any device, and the ability to change access permissions for folders or files that have been shared internally or externally.
ShareSync can be integrated with Digital6 Technologies’ 30 Office in the Cloud™ apps or deployed as a standalone service to complement Office 365™ or other IT environments.
[row][col size=”1/2″ ]RESERVED FOR VIDEO[/col][col size=”1/2″ ]RESERVED FOR LINK TO ARTICLE[/col][/row]
Business continuity with ShareSync
3 steps to getting infected users back to work
If any user in your business gets hit with ransomware, you should instantly close the computer and isolate it from your network. You should absolutely wipe the computer and restore from backup. These are the best practices that will prevent the infection from spreading.
However, if you have ShareSync in place, your users won’t be idled during this process. Here’s how it works.
[row][col size=”1/3″ ] [/col][col size=”2/3″ ]
[/col][col size=”2/3″ ]
Close or isolate the infected computer(s)
Your first priority is to ensure the crypto-ransomware doesn’t spread. Close any computer that’s infected. Cut off network access if you have to—whatever you have to do until you get the infection contained.
[/col][/row]
[row][col size=”1/3″ ] [/col][col size=”2/3″ ]
[/col][col size=”2/3″ ]
Roll back ShareSync’s file archive
Using an uninfected computer, access ShareSync’s admin settings in our HostPilot control panel. Roll back the user’s folders to the moment in time just before the infection occurred. (Watch this video to see how an admin uses ShareSync to perform backup and restore.)
[/col][/row]
[row][col size=”1/3″ ] [/col][col size=”2/3″ ]
[/col][col size=”2/3″ ]
Get back to work using alternate devices
The user can get back to work using any other PC or mobile device. On the PC, they can access their files through ShareSync’s web interface; on a tablet or phone, they can use the ShareSync app. Meanwhile, IT can work on restoring the original device. Any edits the user makes to the files will be synced to the original device as IT updates it.
[/col][/row]
With this kind of business continuity plan in place for ransomware, the benefits are clear:
- For users: Ransomware becomes a mild disruption instead of a major disaster
- For IT: User productivity is restored immediately, so you can carefully focus on containing the outbreak and preventing future infections
- For The Business: Avoid lost sales, angry customers and bad PR
- Plus, no need to pay ransom
[row][col size=”1/2″ ]
Talk to a Digital6 Solutions Specialist about establishing business continuity protection against crypto-ransomware with ShareSync by Digital6 Technologies.
![]()
Or get started with ShareSync today!
(866) 515-4687
[/col][col size=”1/2″ ]
Ransomware resources for businesses
Here are all the resources we’ve put together to help you prevent, contain and circumvent ransomware outbreaks.
[row][col size=”1/3″ ]
VIDEOS
WHAT IS RANSOMWARE?
THE TRUE COSTS OF RANSOMWARE
HOW TO PREVENT RANSOMWARE
CONTAINING RANSOMWARE
TRYING TO PAY THE RANSOM
SHARESYNC: BUSINESS CONTINUITY FOR RANSOMWARE
[/col][col size=”1/3″ ]
DOWNLOADS
PREVENTING PHISHING ATTACKS
INTERMEDIA’S 2016 CRYPTO-RANSOMWARE STUDY
RECOVERING FROM RANSOMWARE WITH SHARESYNC[/col][col size=”1/3″ ]
ARTICLES
RANSOMWARE 101
RANSOMWARE CONTAINMENT TIPS[/col][/row]
